How to monitor Break Glass Account with Defender for Cloud Apps ( MDA )
- Vlad Johansen
- Mar 3
- 3 min read
Good day, everyone!
Monitoring break glass accounts is critical for every company. Fortunately, Microsoft provides tools like Azure Monitor and Defender for Cloud Apps for this purpose.
I have written earlier about how to do this with Azure Monitor here: https://www.need4.cloud/post/how-to-trigger-sms-alert-with-log-analytic-workspace-when-someone-is-trying-to-sign-in-to-an-accoun
Today, I will cover the Defender for Cloud Apps method and create a step-by-step guide. But first, what do we need to get started?
Prerequisites:
Microsoft 366 E5/F5/G5 license or
E3 + E5 Security or E5 Compliance add-on or
Standalone Defender for Cloud Apps license
Requirements:
An active break glass account ( don't need any licenses ) Read here how to create one and about best practices https://www.need4.cloud/post/break-glass-accounts-best-practices
An active account with at least Exchange Online Plan 1 license ( to get an alert )
Microsoft 365 App Connector with Microsoft Entra ID sign-in event component in Defender for Cloud Apps
How to set up Microsoft 365 App Connector in Defender for Cloud Apps?
Log in to Defender XDR portal www.security.microsoft.com with at least Security Administrator role
Go to Settings -> App Connectors -> and press on Connect an app

Find and choose Microsoft 365 from drop down menu
Select at least Microsoft Entra ID Sign-in events from the component list and press Connect Microsoft 365
It can take a while , so please check status after couple of hours.
Now, when your Connector is in Connected state, let's move further
How to setup a alert policy?
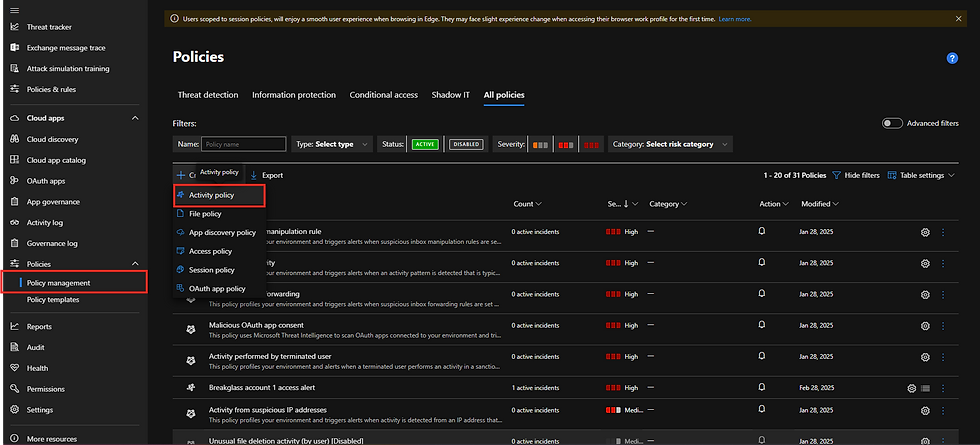
1. Go to Cloud Apps -> Policies -> Policy management -> Press on Create Policy -> Activity Policy
2.
Policy name: Give your policy a meaningful name. For example: Breakglass account 1 access alert
Policy severity: Select High Severity
Category: Select Privileged accounts
Description: Give your policy meaningful description if you want. I'll skip this in my demo
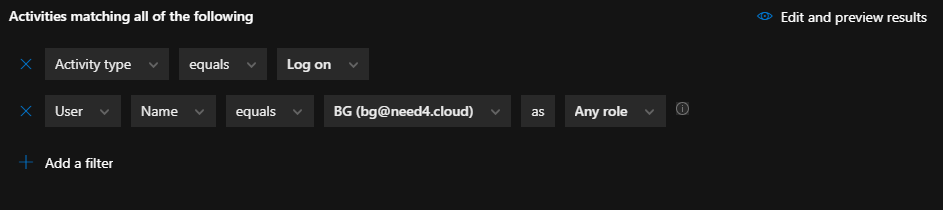
Under Create filters for the policy select Single Activity

Under Activities matching all of the following select following
Activity type equals Log on
User Name equals "select your break glass account" as Any role
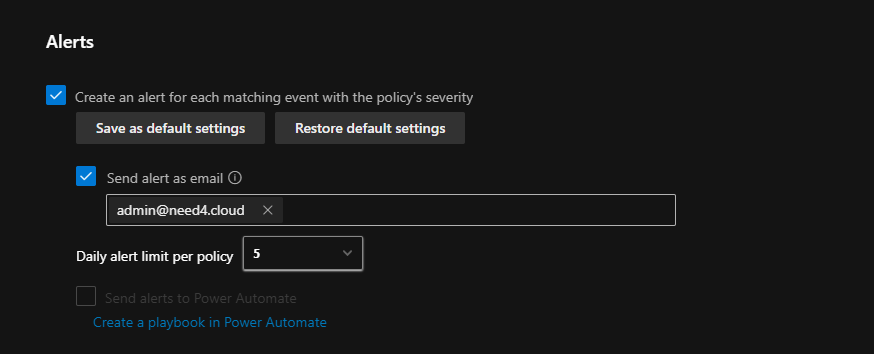
Under Alerts check
"Create an alert for each matching event with the policy's severity"
Check "Send alert as email" and choose the accounts that should receive alerts. One person is not enough. Add, for example, the whole IT department and your external emails as well. You want to be notified immediately, whether you are at work or out of the office.
Set Daily alert limit per policy to 5 , choose what's best for you here. I don't recommend to choose high value here , to avoid to be spammed and miss some important information
Previously, it was possible to send alerts to mobile phone numbers, but this is no longer an option. However, you can still do this in Azure. My tip is to have both alerts active. If one service is down, you should always have a backup method available. Zero-day vulnerabilities are always around the corner. 😊
In Azure Monitor, we have the possibility to get notified about "sign-in attempts." So, if someone tries to sign in to a break glass account, we will be notified. However, with this method, we only get notified about successful sign-ins.
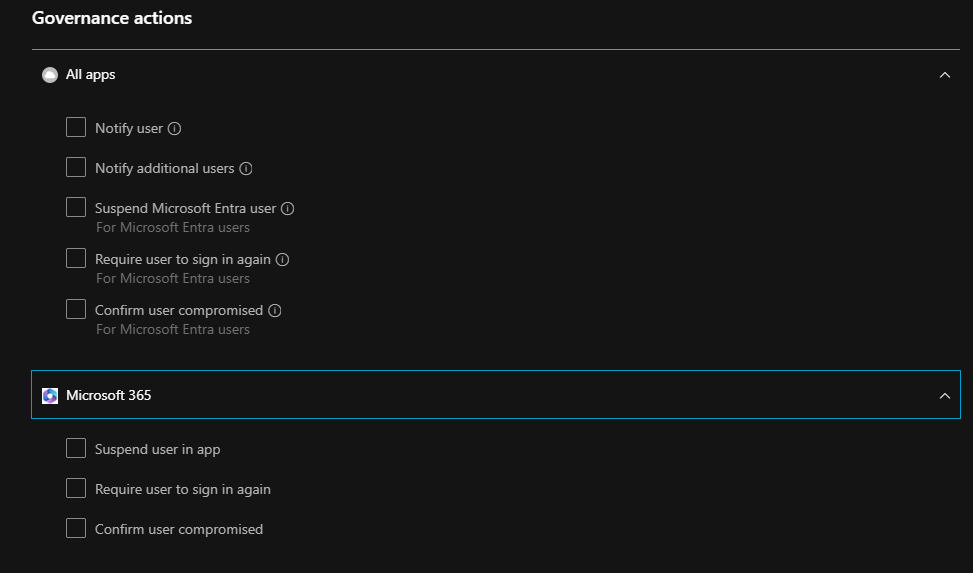
We can also configure additional settings under All Apps and Microsoft 365 if necessary, but in this case, we just want to be warned about sign-ins.
Now, we can Save our policy and try this out.
Sign in to your break glass account, for example to entra.microsoft.com
After about 5 minutes we'll get notified about sign in with an email sent to our inbox(es)
It will look like this

Don't forget to trust the sender :)
Stay secured !

留言